Remote Private Networks (RPNs): Strengthening Home Network Security
In the ever-evolving landscape of cybersecurity, IT managers face the ongoing challenge of safeguarding their organisation’s data, particularly as remote and hybrid work models remain prevalent. Remote Private Networks (RPNs) have emerged as a practical enhancement to existing security measures, offering a structured approach to home network security that mitigates risk beyond traditional solutions.
RPN vs VPN: A Strategic Overview
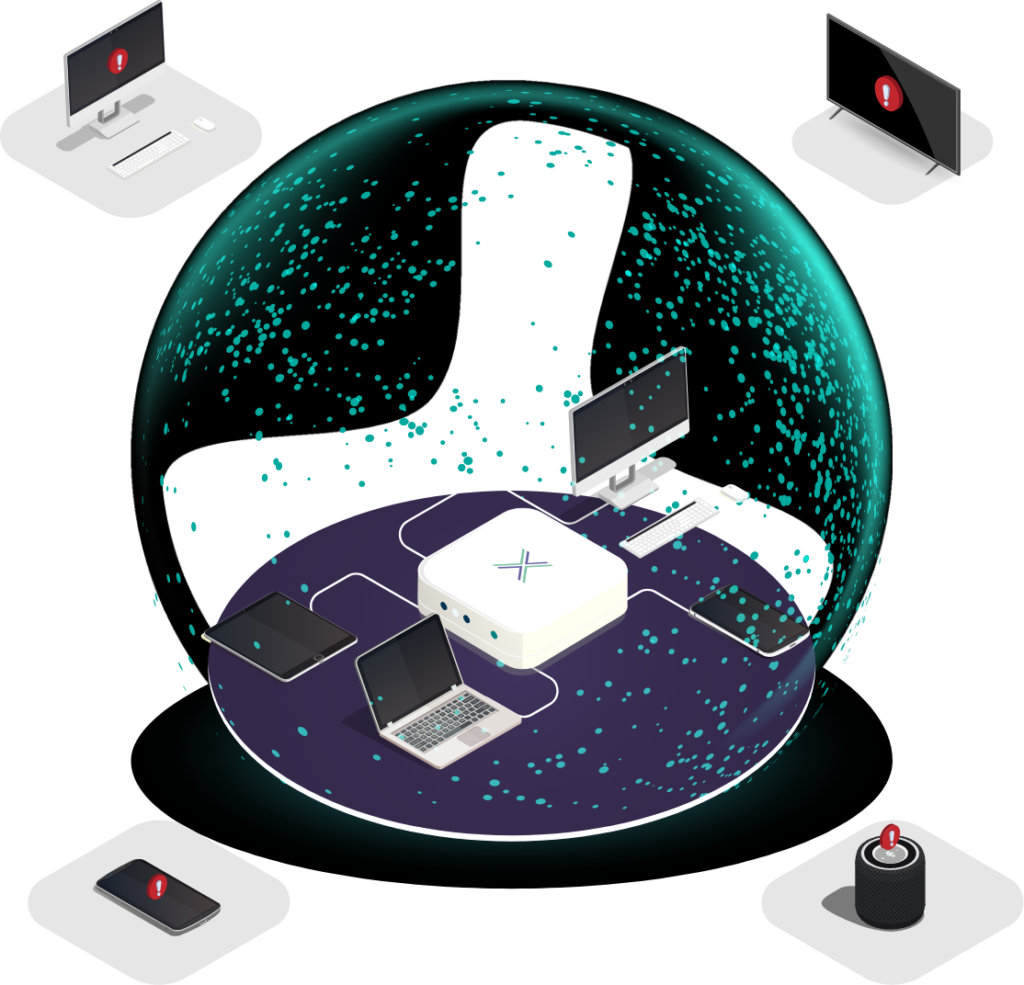
Most IT managers are well-acquainted with Virtual Private Networks (VPNs), which have long been essential for encrypting data in transit between users and corporate systems. VPNs provide IP masking, secure communication channels, and data protection over untrusted networks. However, they do not inherently protect against threats within the user’s local network.
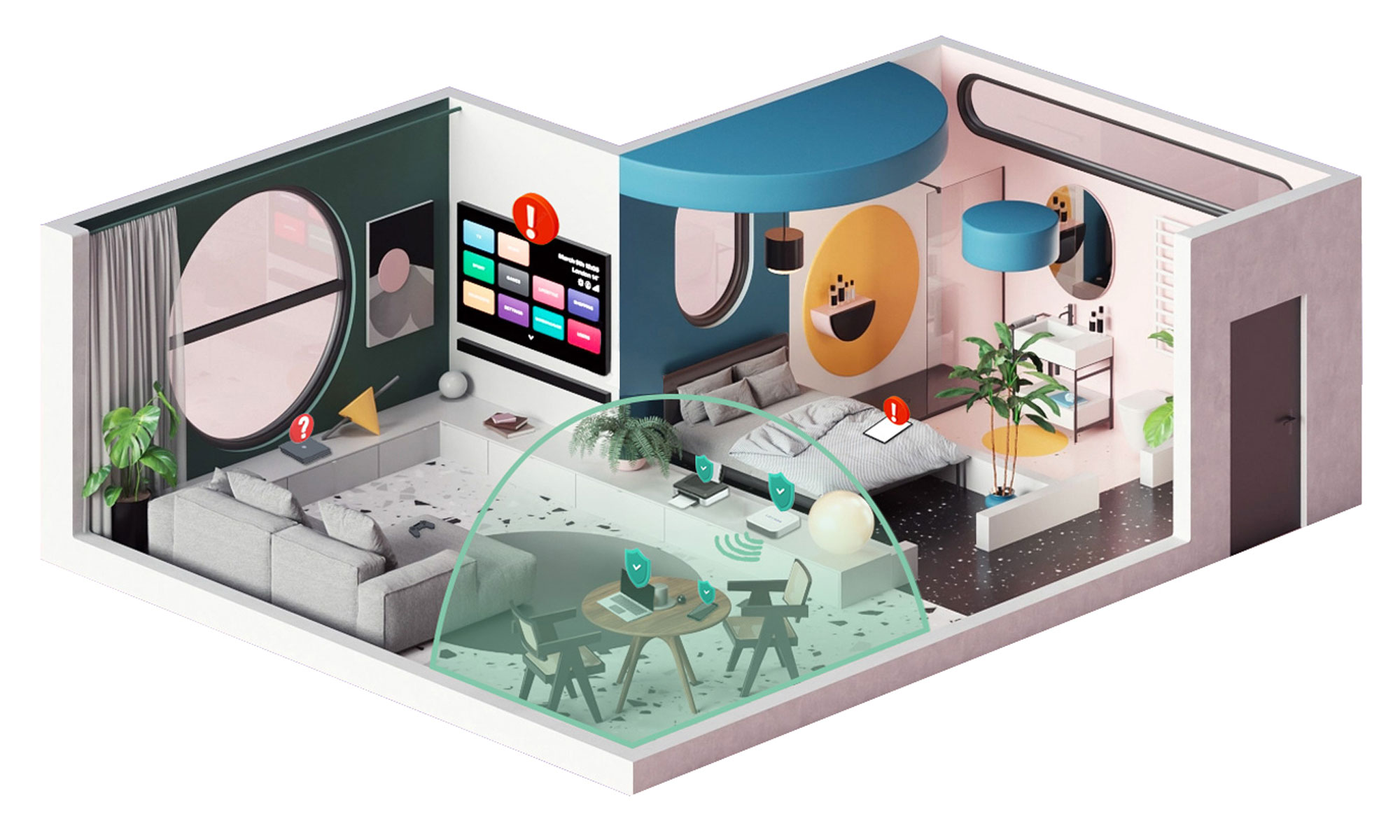
Remote Private Networks (RPNs) address this gap by focusing on securing the environment from which data is accessed. Instead of just encrypting traffic, RPNs establish a separate, segmented network within an existing home infrastructure, isolating work devices from personal and IoT devices. This segmentation ensures that even if another device on the broader home network is compromised, work-related devices remain secure.
Strategic Benefits of RPNs for Organisations
For IT managers responsible for securing complex remote work environments, network segmentation via RPNs provides several key advantages:
✔ Enhanced Security – An isolated network significantly reduces the risk of lateral movement. If a cybercriminal gains access to a personal device on the home network, they cannot move laterally to devices on the RPN.
✔ Optimised Performance – Dedicated work networks experience less congestion, leading to improved performance for business-critical applications.
✔ Simplified Troubleshooting – Issues can be diagnosed and resolved more efficiently within a well-defined, segmented network, reducing IT overhead.
Addressing VPN Limitations
While VPNs are invaluable, they have inherent limitations. They do not protect against threats originating from other devices on the same local network. For example, a compromised smart device on a home network can serve as a launchpad for attacks on other devices connected to that network. RPNs mitigate this risk by isolating work-related activity from potentially vulnerable personal devices.
Moreover, personal devices within a household—whether used by family members or others sharing the network—can pose unintentional security risks. Malware-infected personal laptops, unauthorized software downloads, and even curiosity-driven network probing by household members could inadvertently introduce vulnerabilities. RPNs ensure that these risks do not spill over into an organisation’s work environment.
The Router Firmware Dilemma
A frequently overlooked aspect of home network security is router firmware management. Many users falsely assume that their Internet Service Provider (ISP) automatically updates router firmware, leaving them exposed to known vulnerabilities. Even when users are notified of critical updates, adoption remains inconsistent.
Furthermore, firmware updates do not always address underlying vulnerabilities in software libraries used within routers. This means that even when a router appears up-to-date, it may still contain exploitable security gaps. IT managers face the challenge of ensuring not only that remote workers update their routers but also that the firmware itself is effectively hardened against threats. By segmenting traffic, RPNs provide an added layer of defense, reducing the impact of potential router vulnerabilities.
Conclusion
As the remote work landscape continues to evolve, organisations must adopt solutions that address its unique security challenges. RPNs provide a dedicated, secure digital environment for work-related activities, ensuring that personal devices and broader home networks do not compromise corporate data. For IT managers tasked with enforcing security across distributed teams, RPNs offer a structured, practical layer of protection that complements existing cybersecurity strategies.